TL; DR: Using a unique blend of technologies, Inky’s Phish Fence mail protection gateway shields users from sophisticated phishing attacks. The program alerts users to emails disguised to look like they’ve been sent internally, and detects strange characters and sketchy links, sending users warnings so they’re educated about phishing attempts. The tool is easy to set up and allows administrators access to a dashboard that shows them the threats that exist in their organization.
Ever notice how a lowercase R and N side by side sometimes can look like a lowercase M?
Online attackers do.
Sending emails as Arnazon instead of Amazon is one of the many methods email phishers use to trick rushed or distracted readers into sharing sensitive personal information, according to Kip Young, Director of Marketing for mail protection gateway Inky, who also recounted a recent interaction with a customer who nearly fell for an email that appeared to come from a C-level executive secretary. On closer examination, the message actually came from an external Gmail account.
“You can’t train people to see things the eye can’t detect,” Kip said. “Even if you have all the training in the world, it can be hard to spot these things.”
Phishing attacks are on the rise, and anyone with an email address is vulnerable. Email phishing is the attempt to obtain sensitive information — think usernames, passwords, credit card numbers, and other types of personal data — by sending fraudulent emails and typically impersonating reputable companies or people the intended victim knows.
Fortunately, Inky’s Phish Fence helps block these emails, protects users, and tracks information about recent attacks. The program integrates with popular email clients to warn users about suspicious messages.
“It’s just another way to protect people,” Kip said. “The biggest cyber threat out there is email phishing; that’s how people get into companies.”
Going From Email Organization to Encryption to Phishing Protection
Inky hasn’t always focused on phishing, Kip told us. Founder Dave Baggett started the company as an email client designed to help users organize their inboxes. Inky would automatically categorize incoming mail and enable users to sort messages by relevance.
The platform never quite took off, and Inky pivoted to email encryption and digital signatures. The team found more traction there, but conversations with prospective enterprise clients revealed a much deeper concern about phishing attacks. Inky’s leaders took stock of the email security tools and expertise they had developed and created a new tool: Inky Phish Fence.
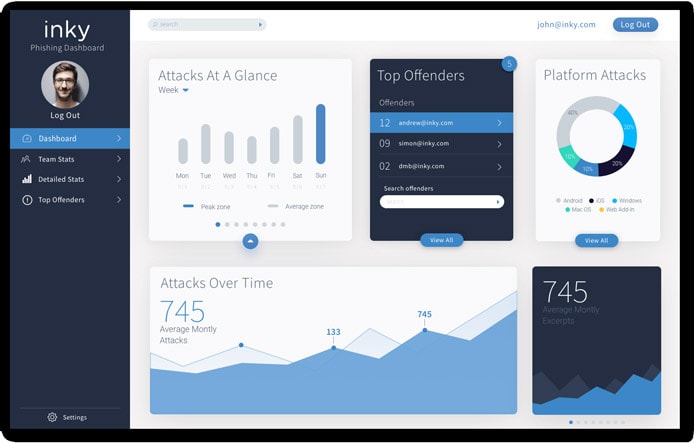
Inky’s dashboard shows administrators exactly what phishing attacks are happening within their company.
Phish Fence is easy for IT admins to configure, Kip said, and they can get users up and running in as little as an hour. The program looks at emails and analyzes the content, headers, and links to warn readers about potential threats.
In addition to warning employees about suspicious emails, Phish Fence also provides administrators a dashboard to see what attacks the company has faced. Inky also provides analytics and insights into the vectors, allowing organizations to easily view phishing data and create reports to share at board meetings.
AI and Computer Vision Algorithms Catch Details Humans Miss
Most companies try to prevent phishing by building awareness. They’ll have employees complete training programs and run simulations, sending fake emails meant to entice people to fall for fabricated scams.
“You get protection, but also a little bit of education,” Kip said of using Inky. “Unlike training simulations, these are the threats happening in your organization specifically. It doesn’t have to be a separate class you take. It’s part of your regular workflow, and you’re warned when things are suspicious in your actual inbox.”
Inky, however, seamlessly integrates into people’s workflow when paired with Office 365, Microsoft Exchange, or GSuite. The software uses computer vision algorithms and artificial intelligence to detect threats that users could easily miss.
“A lot of people will say they use artificial intelligence, but they don’t use it the way we do,” Kip said. “We have a lot of technologists on our staff that know the subject very well. Most machine learning experts, they’re not working on email.”
The computer vision algorithms examine emails as a person would, while also catching things the human eye might miss. For example, someone glossing over the word “Arnerica” might mistake the R and N for an M. (Did you?)
“If someone uses a Latin E instead of a Roman E, your computer might let it through and think it’s fine,” Kip said. “But Inky will say, ‘Wait a minute. Why is this from a different character set?’”
The computer vision algorithms also help expose brand impersonations, letting users know when the logos included in an email don’t match the company sending the message.
“That gets tricky because a lot of emails will have a Facebook logo, but they’re not claiming to be Facebook,” Kip said. “It’s not an easy problem to solve, and logos change over time.”
Inky also uses artificial intelligence to learn a user’s habits and create a social graph. It sends warnings letting users know when it’s the first time they’ve gotten an email from someone, which is useful for fraud prevention since a lot of phishing attacks come from imposters trying to pass as someone close to the intended victim.
Inky Adapts in Response to Client Feedback and Changing Threats
Phishing has evolved, so Inky has had to evolve with it — adapting to attacks as they become more sophisticated, Kip said. For example, attackers know that bad links will get blacklisted quickly, so they’ve come up with ways to quickly generate new bad links.
“It just has to pay off once to be worth doing,” she said.
Inky also adjusts based on user feedback. Originally, the system supplied long-winded explanations about why particular emails were fraudulent. Users said the messages were a bit excessive, so Inky developers added an option that would allow users to read a shorter description and click on a link for additional information.
The program’s button for reporting a phishing attempt also came from customers, Kip told us. Information goes directly to the administrator, who can then learn about the exact threat.
“We always want to hear from people, and we have a really flexible team,” she said. “We’re good about taking feedback and iterating new things. The whole product came from people speaking out about what they needed. We tried solving a lot of things, and this is what people wanted.”
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

