
TL; DR: One of the biggest mistakes businesses make is assuming they’re not a target. Small to medium businesses (SMBs) often have limited security measures, making them vulnerable to cyberattacks, including hacking, malware, and phishing. Phil Wandrei, Director of Product Marketing at OpenText Cybersecurity, shares the importance of having a robust disaster recovery plan (DRP). So, if you’re unsure where to begin your cybersecurity journey, OpenText Cybersecurity’s Disaster Recovery as a Service (DRaaS) is a valuable solution that can help fortify your defenses.
When setting up a business, you have a laundry list of checkboxes. Product and service? Check. Mission statement? Check. Website management? Check. Logo and brand assets? Check. Cybersecurity measures? No check.
Phil Wandrei, Director of Product Marketing at OpenText Cybersecurity, says that small to medium-sized businesses (SMBs) are targeted the most by cybercriminals — and yet, they’re the least likely organizations to have a disaster recovery plan (DRP) in place in the event of cyberattacks, such as data breaches and ransomware.

“It’s the larger organizations that make the headlines in the news, but SMBs are a very lucrative target,” Phil says. “Often, it’s because they haven’t done as much planning as they would’ve liked to or just don’t have the resources to make a comprehensive plan.”
But that’s where OpenText Cybersecurity comes in. As a leader in disaster recovery as a service (DRaaS), OpenText Cybersecurity provides comprehensive security solutions for companies and partners of all.
The 5 Pillars of Protection for Combating Cyberattacks
Although cybercriminals primarily target SMBs, OpenText Cybersecurity aims to help organizations of all sizes be more resilient to cyberattacks. Phil emphasizes that it’s now more critical than ever to have the right plan in place, which is why OpenText Cybersecurity follows five crucial pillars for cybersecurity protection:
- Prevention: Prevent bad things from happening to an organization, such as malware, data breaches, and phishing.
- Detection: Identify the external threats and limit their spread within the organization. It’s also crucial to consider internal threats, especially since between 22% and 60% of cyberattacks are caused by internal members.
- Recovery: If something does happen, the organization needs to recover its systems and data to get back on its feet and return to normal operations.
- Investigation: This step is about digital forensics: discovering how and why the attack occurred — and if there’s a way to bridge those gaps.
- Compliance: Apply your data and knowledge to meet industry regulatory requirements or corporate governance. For example, if you work in US healthcare, you must comply with HIPAA guidelines.
Still, Phil says organizations often overlook the basics even if they have a DRP.
“Have you implemented multi-factor authentication for your internal team? Have you performed security awareness training with your end-users so they can identify suspicious emails?” he says. “It takes more time but pays huge dividends.”
A good DRP has defensive actions to help prevent these attacks, which is exactly where OpenText Cybersecurity’s DRaaS solutions come in handy.
OpenText Cybersecurity’s DRaaS Plans to Protect Your Business Data
OpenText Cybersecurity offers two DRaaS service plans to cater to different business needs. Customers can choose between a traditional software application running in the cloud or a completely managed cloud disaster recovery service.
“Whether a customer wants a self-service or a fully managed service, we’ve got the offerings to help them with whatever they need. It all comes down to how much control and customization they want,” Phil explains.
Traditional DRaaS
The traditional disaster recovery software application allows customers to provide resources since they manage the solution themselves. They can identify what’s backed up and what’s being restored and decide when it’s time to bring those solutions or their systems back online.
Cloud DRaaS
The cloud disaster recovery service is a fully managed service that handles every aspect of your organization’s data and security.
“One of the things we realized in talking with our customers is that their IT staff is minimal,” Phil says. “They just don’t have the bandwidth to provide the staffing and resources if something happens at night or over the weekend, for example.”
The fully managed cloud service allows OpenText Cybersecurity experts to work with the customer to meet their service-level requirements, manage the solution, perform all the testing, and keep their DRPs up to date. Phil says this service is perfect for organizations that need extra support.

If a business experiences a disaster under the fully managed plan, they have to pick up the phone and call their expert team. No matter the time of day, OpenText Cybersecurity has an expert team devoted to bringing those systems back online in the cloud.
The Future of Protecting SMBs from Cybercriminals
Phil encourages businesses to implement a DRP right from the start as soon as they are up and running.
“As businesses are growing and developing, their data is really important, and they just don’t have the time and resources to go back and recreate that,” he says. “Even being offline for a few days can be detrimental, but DRaaS can help prevent that.”
Think of your DRP in the same way that residents in the Midwest have a preparedness and response plan to follow when a tornado siren is activated. The Federal Emergency Management Agency (FEMA) says to immediately find shelter in a basement or storm cellar and stay away from doors and windows. It also recommends building a safe room that meets ICC 500 standards as a preventative measure.
This is how disaster recovery within cybersecurity works, too.
“Even though hardware has become more reliable, natural disasters still happen. There can still be server, storage, power, and network outages,” Phil says. “If an organization has a disaster recovery plan, they can implement their systems and get back online as quickly as possible.”
But if you’re physically away from your resources, operating them remotely during an outage is impossible. Cloud-based solutions can eliminate this challenge by providing reliable access to data and resources from anywhere and anytime.
Interestingly, while the importance of DRPs has always been relevant, their use has evolved over time. As technology evolves and the internet grows, criminals also become more advanced.
It’s not unlike how bank robbers have evolved: Back in the 1930s, for example, it was relatively easy to rob a bank full of people because of the lack of security and technology. But banks now have panic buttons, 360-degree cameras, and action plans, so bank robbers must be in and out within just a few minutes or risk being caught.
Phil says the same can be said for computer security in the “olden days” of the 1980s, ‘90s, and early 2000s. What once started out as inconvenient viruses and worms by individuals eventually became cybercrime with sophisticated ransomware by entire teams.
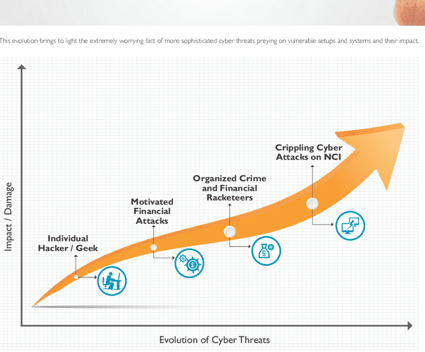
“Companies would backup tapes and move those tapes offsite,” he explains. “So in the event of a disaster, the organization would turn that secondary site on so the staff could manage the data and systems. But as technology improved, it wasn’t cost-effective anymore.”
So, although the concept of disaster recovery as a service is relatively new, its purpose has always been timeless.
This is exactly why organizations are urged to back up their data and enhance their security within the cloud. OpenText Cybersecurity’s DRaaS operates entirely within the cloud because it’s easier to manage, control, and protect.
With cybercriminals getting increasingly innovative and sometimes more desperate, it’s more vital than ever to have a robust DRP. Because as Phil says, “Cybercriminals always look for the weak link in the chain.”
So don’t wait until it’s too late — protect your business today with OpenText Cybersecurity’s self-service or fully managed cloud disaster recovery solutions.



