
While software security can be a vast and complex subject, there are often simple steps that can be taken to immediately enhance security.
Web hosting administration system, cPanel offers a number of options. Plugins and additional security applications also are available.
Here are 10 tips for making best use of cPanel’s security enhancement features.
1. Define Secure Passwords
Change passwords as necessary — strong passwords that cannot be hacked. Use the Password Generator tool in cPanel if you want suggestions.
Define different passwords to avoid the default password configuration that uses the same user ID and password for a user account, FTP account, and so on.
To avoid any snooping around on your password, enable SSL for access to cPanel via “Tweak Settings” in “Server Configuration.”
To avoid hacking of user-level accounts, configure user password strength to oblige each user to use reasonably strong passwords as well.

2. Put Firewall Protection, Anti-Virus, and Anti-Rootkit in Place
There’s no point in tempting fate and just hoping hackers or viruses won’t get into your cPanel installation. CSF (ConfigServer Security and Firewall) is a popular firewall application for cPanel servers. It also gives recommendations about how to increase security.
For anti-virus, ClamAV is available as a plugin for cPanel servers, while rootkit (malicious programs running in stealth mode) detection can be done by installing the Rootkit Hunter software, for example.
3. Secure SSH
Secure Shell (SSH) gives you remote access to the server running cPanel. The command line interface is basic, but sometimes that’s the best way to fix, update, or reconfigure.
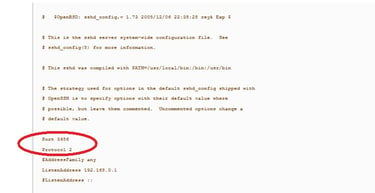
On the other hand, the default port number 22 for SSH is widely known. To prevent intruder attempts, redefine the port number to one that is unlikely to be guessed, such as 1527. Just be sure to pick a port that is not already in use.
Also, modify the system configuration if necessary to use version 2 of SSH (more secure than version 1).
Both of these SSH changes are accomplished by editing the SSH daemon configuration file at /etc/ssh/sshd_config: change the reference to Port 22 to Port 1527 (for example); and Protocol 2.1 to Protocol 2.
4. Always Get the Latest cPanel Updates
When you use the most recent version of cPanel, you benefit from all of the bug fixes and enhancements for security. The makers of cPanel help make this easy by including the “Upgrade to Latest Version” option on the cPanel homepage.
You can then have the server update itself automatically on a daily basis. This is done in “Update Preferences” under “Server Configuration.”
5. Enable Brute-Force Protection
By setting the value of this parameter, you ensure that any repeatedly unsuccessful attempts to access the server from a given IP address will lead to that IP address being blocked.
The IP address will also be logged in the cPanel database.
After a specified time, cPanel will again accept a login attempt to be made from the IP address concerned. To activate this functionality, go to “CPHulk Brute-Force Protection” in “Security Center” and click on “Enable.”
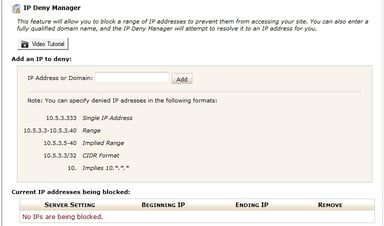
The “IP Deny Manager” option will also allow you to specify a particular IP address, domain name, or range of IP addresses to be blocked from accessing a site managed with cPanel.
6. Disable Anonymous FTP
The risk in leaving Anonymous FTP open is that a hacker will be able to upload content to gain access to your account. By disabling Anonymous FTP and specifying SSL for access (see #1 above), you move two steps closer to proper security.
You can do this in “FTP Server Configuration” under “Service Configuration.” Make sure “Allow Anonymous Logins” is set to “NO.”
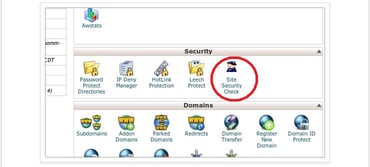
7. Hosted Websites Security Check
Sometimes we focus on shaping and limiting user access to cPanel or the websites it manages, but we forget to check on the nature of the websites themselves. If a domain name has been identified as a potential threat by a tool like Google Safe Browsing, this can reflect poorly on your organization’s reputation and possibly its revenue and profitability.
The “Site Security Check” function in cPanel checks to see if this has happened to any of the domain names linked to websites being hosted.
8. Securing Apache and PHP
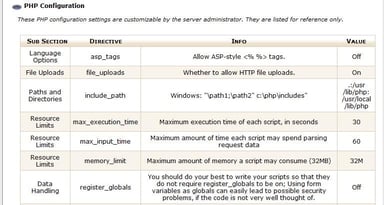
For rapid building and compiling of new versions of the Apache server and PHP scripting language, cPanel includes a utility called, “EasyApache.”
Besides practicing proper security by ensuring the latest versions are being used, you can also contain any potentially malicious PHP scripts within their home directory to prevent them from opening files elsewhere.
To do this, go to the PHP open_basedir Tweak command in the “Security Center” and check and save “Enable php open_basedir Protection.”
9. The Tweak Settings Checklist
As well as the specific settings discussed above (e.g., requiring the use of SSL), the “Tweak Settings” section in “Server Configuration” offers a range of other security options. These include the use of Cookie IP validation (limit the possibility for hackers to capture cPanel session cookies and attempt to access cPanel), the use of security tokens to access cPanel, and the “Bounce” option to discard inroutable emails and thus protect the server against mail attacks.
10. The Security Center Checklist
In addition to the password strength options and containment of PHP scripts (with open_basedir), other security enhancement options include disabling compiler access for unspecified users, limiting use of the su command to become the root user, and defining “Shell Fork Bomb Protection” to prevent users from gaining unlimited access to server resources.
As you check out these different ways to reinforce security, you’ll see more of the security enhancement options available to you in cPanel.
Take a moment to read accompanying instructions, see what the options do, and understand how they too might help you run a secure, high-performance cPanel server.
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

