
TL; DR: Your infrastructure is under constant risk from external and internal threats coming from every direction. Being proactive to mitigate these dangers is increasingly important, and the cornerstone of an active defense is intelligence. Nagios XI, HostingAdvice’s Developers’ Choice™ award recipient for providing comprehensive IT management, delivers robust, instantly actionable intelligence that helps your organization fully understand its current condition through server and network monitoring and real-time data audits. Identifying and defending against all manner of threats and helping you repel and prevent damage and insurgency makes Nagios a powerful ally in the internet war zone.
The Internet is a war zone. When your network goes online, it’s stepping into the center of a battlefield with threats looming in every corner. Browser attacks are like bullets, flying at your users and servers from all sides, in a dozen different calibers. Compromised-key attacks, man-in-the-middle data interceptions, and Distributed Denial-of-Service (DDoS) pose as constant dangers to your online livelihood.
Every automated defense is eventually countered by the invisible enemy. Secure Sockets Layer (SSL) was the armor donned to protect against the most common automated threats, but in 2016, SSL attacks rose 11%, according to the McAfee Labs Threat Report.
Maintaining safety means your IT department must be simultaneously war council, counter-insurgency unit, and field hospital to limit damage and perform emergency surgeries on your system. This is accomplished by feeding the defense planning and counter-insurgency functions with actionable intelligence. That’s what the Nagios IT infrastructure monitoring platform brings to your arsenal. It’s also why HostingAdvice has recognized Nagios XI our Developers’ Choice™ award for comprehensive IT management.
An IT department acting too often like a MASH unit can’t support its defense and counter-insurgency efforts, and thus becomes a sinking ship, plugging holes that only multiply in quantity and frequency. Nagios XI is an effective tool in maintaining your defenses.
Nagios XI in a Nutshell: Comprehensive IT Infrastructure Management
Nagios XI is complete infrastructure monitoring, keeping tabs on the state of servers, networks, and applications. Like your own CIA counterintelligence analyst, it looks for unusual traffic patterns and levels in your applications, services, operating systems, network protocols, system metrics, and infrastructure. The software helps you identify attacks early, when you have only a few soldiers beating on your walls — before your systems are surrounded by the hordes.
Through sensitive, customizable network monitors, Nagios XI even lets you see pre-attack indicators, making note of the subtle signs of enemy reconnaissance agents lurking in the dark just beyond the view of your normal camp sentries.
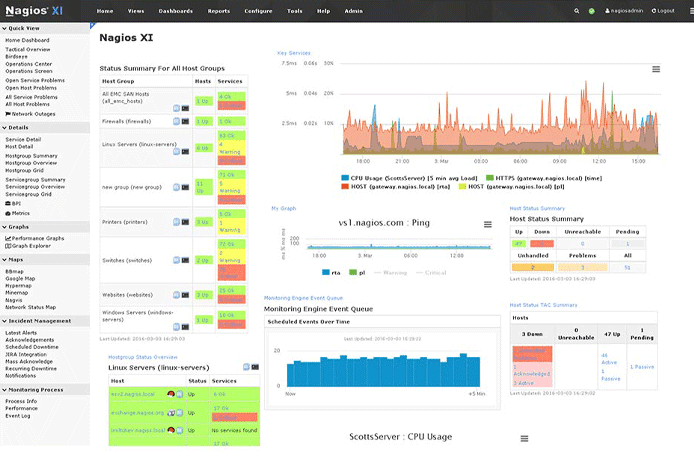
Nagios XI includes a new user interface that provides a customizable overview of your operations.
It doesn’t only look outward. Nagios XI is also an X-ray view into your own organization’s operations. By enlisting the aid of specialized operatives from a pool of hundreds of third-party add-ons, such as NCPA, JSend NSCA, and Birdseye, you can identify, monitor, and excise threats that have already made it past your defenses.
You can also identify internal problems in their early stages. Data leaks and human-initiated network compromises are made visible and rooted out before they pose a genuine security risk.
Nagios Log Server™ Makes Finding and Auditing Data Simple
Monitoring the operations of your infrastructure is accomplished through adroit auditing in an agile data log system. Nagios Log Server is that dexterous system.
You can query your log data in hundreds of different ways, identifying the vector of any current or former threat. Once the entry point is found, the Nagios Log Server data will let you trace the trajectory of the threat to its end target. You can then insulate the rest of the systems from that compromised user, system, protocol, or application while you cure it.
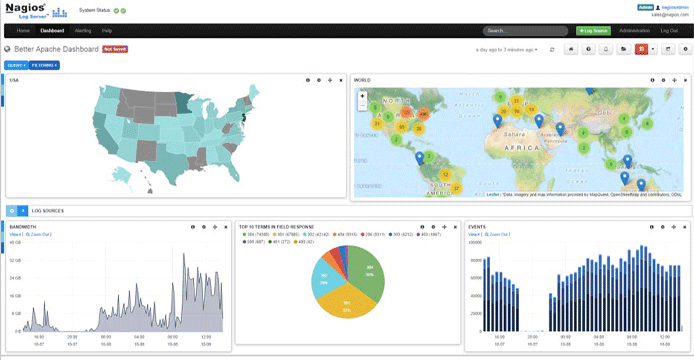
The dashboard for the Nagios Log Server keeps tabs on every incoming event and is easily shareable with co-workers.
By using the advanced customizable alerts built into Nagios Log Server, you can do better than cure an attack — you can repel it in real time. The tool identifies precursors to outside incursion and internal compromise and alerts you to them instantly.
That gives you the chance to act on the intelligence in time to prevent any actual damage. Instead of quarantining and curing a compromised user, system, protocol, or application, you can prevent that target from ever being reached. And, in many cases, you can inoculate the rest of the infrastructure before the initial breach becomes an actual infection or system damage.
Nagios Network Analyzer™ Shows Network Activity and Health in Depth
Responding to and guarding against threats is only part of the task of infrastructure management. It’s also crucial to monitor the general health of the network to facilitate normal operations.
Nagios Network Analyzer is like optical-enhancement, adjustable-zoom field binoculars providing network administrators a crystal-clear look into their network traffic and traffic sources. It uses both sFlow and JFlow sampling and measurement for pixel-accurate insight at 500x magnification.

Nagios Network Analyzer ensures the security and reliability of your system through traffic and bandwidth monitoring.
Twist the focus wheel one way to peer into network traffic to identify its ebbs and flows and reallocate resources during unexpected peak activity.
Spin the focus wheel a little more to see past the levels of traffic into its sources to identify which applications, network protocols, and servers are sending and receiving too much, too little, or just enough data. Crank it even further to zoom into views of the data used by individual access points, users, and queries.
Defend and Understand Your IT Infrastructure with Nagios as an Ally
Your infrastructure is constantly at risk from numerous external and internal threats, with more appearing daily. Nagios XI is complete infrastructure monitoring, keeping tabs on the state of servers, networks, and applications. Nagios Log Server lets you find and audit data with ease while allowing enough time to be actionable, particularly with its robust alert system. With the Network Analyzer, you can easily monitor and maintain the health of your network through accurate sampling and measurement.
Mao Zedong famously said, “the only real defense is active defense.” Defending your organization’s infrastructure means a vigilant IT department actively monitoring and constantly evolving that defense. When talking about the freedom and integrity of data systems and IT infrastructure, the best defense is intelligence.
Nagios XI provides deep intelligence that helps your organization understand its current condition, including health and defense, as well as plan for future operations and counter-insurgency, which is why they’re our Developers’ Choice™ for comprehensive IT management. According to Alex Syse, Nagios’s Marketing Strategist, the company shows no signs of slowing.
“Our team at Nagios Enterprises has been working vigorously to take our solutions to new heights,” he said. “We have some great new features in our development pipeline and cannot wait to share them. Uptime is more critical now than ever, and we are proud to help thousands of companies worldwide save time and money in their fight against IT threats.”
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

