
TL; DR: Imperva is a time-tested cybersecurity provider on a mission to protect user data and applications regardless of whether they are stored on-premises or on cloud servers. The company’s solutions accurately detect, evaluate, and block incoming threats while empowering customers to manage business-critical risks. Ultimately, Imperva’s goal is to defend the businesses of its customers today — and be by their sides as they grow through digital transformation strategies in the future.
Data privacy has been top of mind for businesses worldwide in recent years, particularly as laws such as the European Union’s General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) have come into force.
Compliance with such regulations — intended to give individuals control over their personal data — is essential to maintain a good business reputation and avoid stiff penalties.
But if businesses think data security ends with compliance, they’re sorely mistaken. That’s according to the folks at Imperva, a cybersecurity provider that has been in business for nearly two decades and serves some of the world’s biggest companies.

Imperva takes a holistic approach to edge, application, and data security.
“Today’s businesses know that they need data security strategies — unfortunately, most companies will look to regulations to determine what they absolutely have to do, such as securing a set of databases for PCI compliance, and they don’t go much beyond that,” said Terry Ray, SVP of Imperva. “That’s the battle that we fight: to help organizations understand that there’s more to data security than compliance.”
Terry said he’s seeing some businesses make changes in that regard, such as appointing a Chief Security Officer (CSO) or Chief Information Security Officer (CISO) to handle data security, rather than the compliance and internal audit teams of five years ago.
Whatever stage of digital transformation a business finds itself in — whether it stores data in legacy on-premise datacenters or cloud servers — Imperva’s goal is to detect, evaluate, and block threats. And in today’s world, that means safeguarding vulnerable data, whether regulations govern it or not.
Protecting Assets from Ever-Evolving Cyber Crime Techniques
Imperva, headquartered in San Mateo, California, was founded in 2002. Prior to founding the company, Shlomo Kramer served as Co-Founder of Check Point, an international provider of security-focused hardware and software.
“There was a significant spike in not only threats against web applications, but also successful attacks on web applications, to the degree that Shlomo Kramer started having conversations with ethical hackers in the electronic pen-testing space,” Terry said. “He asked, ‘How often do you succeed when somebody asks us to penetrate a website?’ and they said, ‘We have never failed — we get in 100% of the time.’”
Back then, solutions were based squarely on patching code. That was fine if a business authored its own proprietary solutions, but that’s not the case with commonly-used third-party apps.
“It’s great that you can fix the things that you wrote, but what if you also embedded third-party code via OpenSSL, WordPress, or Joomla, etc., and you can’t fix it,” Terry said. “You’re at the whim of that developer or company to decide if and when they want to patch their code.”
Shlomo realized he had an opportunity to build a business and also change the direction of how companies perceive risk when it comes to their applications.
“However, he took it a step further than the web frontend, considering what happens when that web application is breached,” Terry told us. “For example, a cybercriminal can make it so that you can’t get to your web application through DDoS attacks, they can make it so that when you get to your application, you see something else (defacement), or they can access your actual data in the backend through the authorized user of your application.”
Imperva’s solution was to address all concerns through product design to protect data as well as all possible paths leading to it, including the edge of a network and the databases that sit on servers behind web applications. Today, the company’s multicloud platform protects users from more than 18 billion attacks per month.
Solutions to Identify, Evaluate, and Eliminate Threats
Terry told us the Imperva team initially built its platform to solve for a significant gap in the marketplace in terms of application and data security. Over the next 18 years, the team witnessed a rise in data exfiltration crimes and realized they still had work to do.
“Even today, these sorts of threats occur because organizations depend on checkbox-type technology versus best-of-breed solutions,” he said. “Or, maybe they have solutions deployed on the data side but don’t have any visibility to the application side. Every single day, if you search, you’ll find a new breach.”
Imperva’s cybersecurity platform and end-to-end solutions address application security, breach prevention, cloud security, database security, DDoS protection, and file security, among others.
One of the company’s newest releases, Imperva Cloud Data Security (CDS), expands its application and data security solutions to provide visibility and ensure compliance for data hosted on cloud servers by a database-as-a-service (DBaaS) provider. The SaaS solution makes onboarding a matter of minutes and includes automated discovery, classification, continuous monitoring, and security insights.
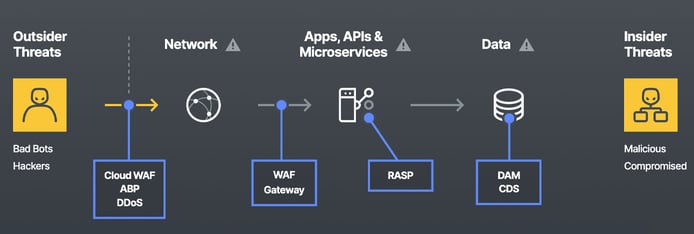
The end-to-end solution safeguards against internal and external threats, plus everything in between.
Terry told us that Imperva’s goal with all of these tools is to provide a server-agnostic solution to suit all users.
“Wherever your applications are — on-prem, in Amazon Web Services (AWS), Google Cloud Platform (GCP), Azure, Alibaba Cloud — it doesn’t matter because your traffic is going to come to us first, and we’re going to cleanse it,” he said. “If it’s a DDoS attack, we’ve got over six terabytes of overall capacity to protect you. Cloud licensing is built around capacity consumption, but you don’t have to worry about going over capacity because we can remove bad traffic before it gets to the cloud.”
Reduce the Risk of Breaches and Noncompliance Alike
Imperva screens 1.14 trillion connections every month for malicious traffic.
“The statistics we have on that traffic show roughly 30% of all traffic to any website is bad bot traffic, which means if you’re paying $100 a day for AWS, $30 of that is spent on bad bot traffic that doesn’t belong,” Terry said. “If you can get rid of it up front, then you’re automatically seeing a return on investment.”
The company’s technology also provides value on the data security side in terms of reducing the cost of noncompliance as well as building and maintaining a good reputation with customers.
“Whether helping users avoid fines from the Federal Trade Commission or brand damage and customer loss, we reduce risk on the database side,” Terry said. “We also provide full visibility into and access to the data.”
Terry estimates that in 9 out of 10 breaches, organizations don’t know who accessed the data, what was accessed, or how much because employees typically turn off data logging to boost performance.
“Our technology was built so that organizations do not have to turn on database logging,” he said. “We capture logs ourselves so they can leave the logging turned off, which saves them man-hours that would be spent on forensic research investigation if there were a breach or audit.”
Helping Orgs Address Data Security Amid Digital Transformation
Over the past year, the Imperva team has turned its focus to helping customers as they transition to cloud-based infrastructure.
“We’ve worked to use technology to change the general mindset on securing data in the cloud,” he said. “Data security has always been perceived as being complex and hard to implement.”
Imperva’s answer, the aforementioned Cloud Data Security product, meets requirements specified by customers, such as scalability and turnkey services, to help change that mindset.
“It’s so simple that you can spin it up in 30 minutes — the time it takes you to get the information you need from AWS,” Terry said. “Once you have that information, we’re classifying, we’re automating, we’re monitoring, and we’re telling you what’s happening. We’re truly transforming the data security model in a way that matches their experience with the rest of the cloud.”
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

