
TL; DR: Secureworks has been delivering trusted managed IT security services to organizations worldwide for nearly two decades. In 2018, this leader in the intelligence and web security space teamed up with Carahsoft — the large government IT solutions provider — to help government, educational, and business organizations mitigate online threats. The Secureworks-Carahsoft Alliance was built with the fundamental goal to give organizations the early warnings and real-time threat intelligence they need to prevent security breaches and protect their data.
With recent concerns over Russian involvement in spreading propaganda on social media channels, Facebook, LinkedIn, and other platforms are more concerned than ever with verifying user profiles. Despite legal-name-only policies and SMS verification procedures, hundreds of fake accounts continue to exist on social media.
While the majority of these accounts are easily distinguished from legitimate profiles, a few of them have managed to fool even the highly-trained professionals of major organizations. In late 2016, a string of online attacks against a variety of organizations in the consulting, technology, oil and gas, telecommunications, and aerospace industries was launched by an Iranian espionage group known as OilRig/Cobalt Gypsy. The group targeted mid-level technicians, likely for their perceived elevated access to their corporate environments, through the fake profile named Mia Ash. Mia Ash, listed on LinkedIn, Facebook, and other sites as a professional photographer, established relationships with her victims and convinced some to open malicious files that may have allowed access to the victims’ credentials and possibly their corporate network.
In one case, the espionage group convinced an unsuspecting employee of a consulting firm to open a malicious file on his work computer. Although the infection was mitigated before it could spread to the wider company network, the incident served as a wake-up call for web security professionals everywhere.
Leading the investigation into the Mia Ash attacks was Secureworks, a US-based digital security organization. Secureworks’ Counter Threat Unit™ (CTU) research team believes the threat actors may have been politically motivated, possibly working on behalf of the Iranian government.
Since its inception nearly two decades ago, Secureworks has uncovered multiple malicious hacker campaigns targeting organizations in the financial, retail, healthcare, technology, government, and energy sectors by numerous nation states and criminal adversaries, including the infamous phishing campaign launched against high-ranking staffers of the Democratic National Committee (DNC) and Hillary Clinton for President campaign. Secureworks also discovered a link between the North Korean government threat actors, the Lazarus Group, and the far-reaching WCry Ransomware campaign.
A New Partnership Created to Address Evolving Security Needs
Secureworks was founded in 1998 as a privately held company. In the years that followed, Secureworks would merge with LURHQ Corporation — another managed security services provider — and acquire the Managed Security Services business from VeriSign. With these partnerships came a much larger client base spanning over 50 countries from Taiwan and Saudi Arabia to the UK and Mexico. Later, in 2011, Dell acquired Secureworks and the company eventually moved into the Australia, New Zealand, and Japan market, becoming a truly global security brand.
Meanwhile, Carahsoft, a Virginia-based IT solutions company, had emerged in the mid-2000s to connect government agencies and educational institutions with top-of-the-line security solutions. And, in 2018, Carahsoft teamed up with Secureworks to satisfy mutual interests.

Secureworks’ Steven Rich said the Carahsoft partnership was created to help the IT solutions company protect its clients.
Carahsoft, which partners with several other companies to provide services to clients, lacked security-related services prior to the partnership. And Secureworks knew it could benefit from Carahsoft’s compliance and reporting solutions aimed at the public sector.
“We were a natural fit,” said Steven Rich, Director of Secureworks North American Public Sector Activity. “We now have a partner that has experience in managing large national government contracts, like GSA.”
General Services Administration (GSA) contracts contain predetermined prices and conditions to simplify purchases at the federal level.
A Monitored and Managed Approach to Safeguard Large Organizations
As a provider of managed security services, Secureworks, together with Carahsoft, offers organizations some of the most powerful security solutions in the world. Secureworks makes this possible by leveraging advanced threat intelligence made up of internal expertise and industry insights developed from investigations into threats such as the Mia Ash and DNC attacks.
As a result of its thorough threat analysis, Secureworks is capable of offering some of the highest-level security services in the world, recognizing threat actors and their tactics far in advance.
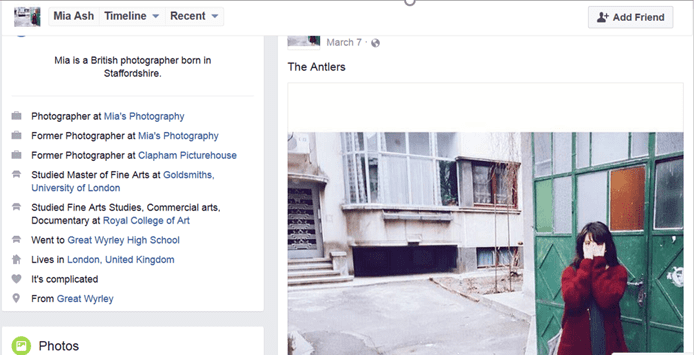
Threat actors used the fake Mia Ash profiles on LinkedIn and Facebook to convince victims to open malicious files.
Not only is Secureworks’ advanced threat intelligence a major factor in its own success, but it also plays a big role in its clients’ success.
“Our hands are all over the place as far as research goes, but at the core of our services is a monitored, managed approach,” Steven said. “We monitor the firewall — which is the front door — and then we monitor access points all over the network, looking for events that don’t look right.”
Once questionable information or settings are detected, businesses are given contextual alerts and hands-on remediation assistance. In addition, Secureworks helps clients reconfigure their networks and put preventive measures in place to safeguard against future threats.
Providing Real-Time Threat Intelligence and Countermeasures
Aside from its extensive research into some of the world’s biggest malicious hacking incidents, the company’s cascading-network approach is another major factor in its efficacy. Once isolated threats are identified and analyzed, the CTU researchers and security analysts search for similar threat signatures and tactics within the networks of other clients.
“When we see one threat hitting, say, against a financial client, we can take those indicators and put in a countermeasure to look for that kind of behavior with all of our financial clients,” said Elizabeth Clarke, Secureworks Director of Media Relations. “We use that intelligence to gather how these threat actors go after their victims. If it works, they’re going to use it again.”
Recognizing suspicious behavior is more critical than ever, as many malicious hackers now choose to forego the use of malware and employ more covert tactics such as social engineering. That’s why Secureworks offers managed security solutions such as data breach protection, risk consultation, and compliance management.
Secureworks’ solutions include, among others, managed firewall, malware detection and intrusion prevention, web application scanning, and endpoint security. These solutions can be used to protect clients’ data and applications residing on-premises or in the cloud.
Powering Secureworks’ offerings is the company’s Counter Threat Platform™ (CTP), a security-event analysis engine that processes as many as 250 billion events a day. With its global visibility, Secureworks can identify new threats targeting specific industries and geographies, and help organizations predict, detect, prevent, and respond to them. Combining supervised machine learning with the expertise of more than 800 researchers, analysts, responders, and security consultants, the Counter Threat Platform offers actionable insights into network vulnerabilities, as well as security ops for IoT and other innovations.
The Aim: To Conduct Continuous Research to Protect the World’s Data
Real-time Threat Intelligence and research are at the heart of all Secureworks’ solutions. Unlike conventional approaches that consist mainly of software suites and a few consultation services, Secureworks takes a hands-on approach, doing the bulk of the work for its clients through extensive research, real-time threat-intelligence gathering, continuous threat hunting, and analysis.
Aside from sending alerts and intel, the CTU regularly arranges calls with clients to discuss vulnerability issues and their solutions. For well-known threats and vulnerabilities, the contextual information shared with clients is largely gathered by research on past incidents from the same or similar threat actors, malware, and tactics. For emerging threats that might have slipped past other security tools, Securworks employs its continuous online threat hunting, Active Threat Hunting, in combination with its around-the-clock endpoint monitoring technology Red Cloak. The Active Threat Hunting service is performed by Secureworks’ Senior Intrusion Analyst (SIA) team (its most seasoned threat hunters) who work closely with an organization’s security team to continually hunt for threat actors who might have gained a foothold into an organization.
Combining the 24x7x365 monitoring and customized hunting with threat intelligence from Secureworks’ Counter Threat Unit™ (CTU) research team, Secureworks is able to provide businesses with the earliest possible warning that one or several of its endpoints might be compromised. Clients are also provided with all the details needed to determine the impact of an attack, which in turn helps accelerate the remediation efforts and makes more efficient use of a company’s security team by pinpointing exactly which systems are compromised, how they were compromised and how they can be repaired.
By investigating the methods of some of the world’s most infamous threat actors, the CTU has uncovered a wealth of insights regarding some of today’s most lethal online threats, including ransomware, banking trojans, and digital espionage.
Dubbed “Iron Twilight” by the CTU and, alternatively known as “Fancy Bear”, the espionage group behind the DNC and the Hillary Clinton Campaign attacks, has been on Secureworks’ radar since 2015.
“We were confident that they are affiliated with the Russian government because of some of the tools they used, along with their targets, tactics, and procedures,” Elizabeth said.
Following a trail of registered bit.ly links, which when clicked on led to a fake Google login page which was prepopulated with the victim’s Google username, the CTU recognized some of the email addresses in use as those of people involved in the DNC and the Hillary Clinton Campaign for President. Additionally, the CTU recognized the domain registering the bit.ly links as it had been used in previous cyber campaigns conducted by Fancy Bear. In total, over 19,000 bit.ly links were created by the Russian hackers to target some 4,700 people around the world. By using covert phishing tactics, Fancy Bear was able to fool numerous high-level campaign staffers and government employees in the US, into revealing their Gmail passwords using very legitimate-looking page renderings.
Given the already high priority that online security takes in our lives, the fact that even highly-secured organizations like the DNC could fall victim to such a digital attack is alarming. To combat these incidents and make online operations more secure, the bulk of the CTU’s work involves digging deep into incidents of the past and present, as well as anticipating possible future exploits. As such, Secureworks’ mission is to conduct continuous research, threat hunting, and threat intelligence gathering and share its insights with clients. With numerous investigations currently being conducted, their corresponding reports are to be made public at the upcoming RSA Security Conference in April.
By enabling clients to better shield themselves from attack, Secureworks helps make the world more secure. Safeguarding organizations, government agencies, and much of the Fortune 100, Secureworks is one of the most trusted names in digital security — and with good reason. Since 1998, the global leader has secured hundreds of businesses in over 55 countries and was the first organization to gain significant insights into some of the world’s most devastating cases of online financial crime.
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

