
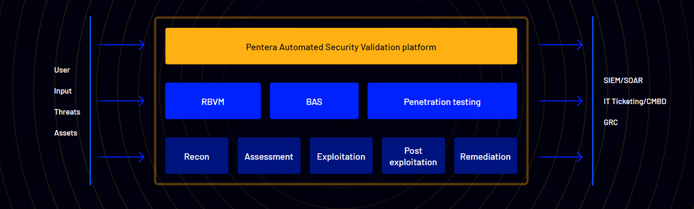
TL; DR: Pentera (formerly Pcysys) is changing the landscape of cybersecurity defense with its automated penetration testing and security validation platform. Pentera delivers a decision engine with multiple attack frameworks that expose real-time vulnerabilities within an IT infrastructure. The approach involves ethically and safely hacking into a network using malware injections and activation capabilities. The result is continuous coverage that accelerates the validation and remediation cycle by exposing risk-bearing weaknesses as they are created, thereby reducing third-party reliance and expenses, and increasing the efficiency and efficacy of security teams.
Nearly a decade ago, Arik Liberzon found himself working as a red team and penetration test leader in an elite cyber warfare group in the Israeli Defense Force. The IT infrastructure he was managing was so vast that once he and his cybersecurity defense team had evaluated a section of the infrastructure for a particular unit, that section would not be reevaluated until a full 12 months later. For Arik, this lack of continuity posed an obvious problem.
Arik said that he realized providing consistent validation on a continuous basis across an IT infrastructure so large was a near impossible feat. Even the most advanced red teams needed support beyond just hiring extra people, who may approach the same problem with a different skill set or perspective.
This led Arik to begin to conceptualize — and design — an automated penetration testing platform that approached a network from an attacker’s perspective. And this ultimately, with the help of Co-Founder Arik Feingold, resulted in the launch of Pcysys (now Pentera) in 2015.
According to Maor Franco, Senior Director of Product Marketing for Pentera, Arik’s initial vision was met with much skepticism among his peers.

“People told him, ‘So wait, you’re going to model the penetration tester’s mind into technology?,’” Maor said. “They told him he’s crazy, that it’s impossible, you need the human element in it. But that’s the mission Arik set on.”
Arik’s vision developed into his building a decision engine with multiple attack frameworks designed to approach an IT infrastructure from the attacker’s perspective, as opposed to the more traditional defender’s perspective. This was accomplished by ethically hacking into a network in a safe, harmless way, using malware injections and activation capabilities.
“What Arik did is pretty amazing,” Maor said. “Think about it from an attacker’s perspective and their arsenal: ‘I want to progress the attack.’ So the engine knows to autonomously move around the network whenever it finds a weakness trying to escalate and exploit the vulnerability in real life, all in a safe manner.”
Pentera Exposes Security Gaps in Real Time
Pentera’s Automated Security Validation (ASV) allows companies to continuously run performance security validations in a consistent, real-time, continuous manner. This differs from traditional service-based penetration testing, which may pinpoint security threats and vulnerabilities accurately in a specific, point-in-time basis, but cannot be applied in real time or run continuously. By safely and ethically hacking into an IT infrastructure, Pentera’s ASV shows how a hacker can challenge a network’s security controls. That way, real vulnerabilities and security gaps are identified and treated before they are exploited.
“The entire security industry mainly focuses on the ‘kill chain,’” Maor said. “The attacker starts, the attacker ends, mission accomplished. Proactive security is when you’re doing something outside of the kill chain. You need to live-test all of your infrastructure and potential security weaknesses the same way the adversary would — ahead of time. We’re outside of the kill chain, so you can identify the root cause before maliciously exploited, and cut it at the root.”
Pentera’s cyber-offensive, real-attack approach allows cybersecurity teams to accelerate the validation and remediation cycle by focusing first on mitigating breachable, risk-bearing vulnerabilities and weaknesses as soon as they are created.
With a single mouse click, Pentera’s agentless, low-touch, fully automated security validation allows clients to check at any time whether their IT infrastructure is secure and quickly identify the issues that need to be addressed based on the severity of their potential breach outcome.
By exposing the present security gaps within an organization’s infrastructure, Pentera’s ASV technology allows users to quickly treat vulnerabilities before they are exploited. This paves the road to cost-effective remediation that reduces expenses and reliance on third-party intervention.
Pentera’s ASV Delivers an Automated Red Team
Since its founding, Pentera has amassed a loyal client base of over 350 companies worldwide, ranging from organizations as large as the global investment giant, Blackstone, to smaller companies specializing in everything from healthcare to retail and higher education.
Our current technology is industry agnostic,” said Arik Liberzon in a 2019 Safety Detectives interview. “A network — is a network — is a network. Even cyber-security technology companies buy our product to ensure their network is resilient to all the latest cyber threats.”
Regardless of a company’s size, or scope, Pentera’s ASV platform provides clients with automated, continuous security testing and validation, as often as needed, at a fixed cost.
For larger companies, such as Blackstone, with a cybersecurity red team on staff, ASV can be used to add or augment red team activities. That can offload red teams to focus on other areas more integral to that company’s business mission.
For smaller companies that may not have the means, or the need, for an in-house red team, Pentera’s ASV platform can provide the continuous, on demand coverage of a cybersecurity red team on staff.
Pentera’s model for continuous, automated security validation is designed to be practical, attainable, and save companies time and money. But not at the expense of replacing the human element.
“Some vendors may say, ‘My tool can save you people.’ That’s a mistake,” Maor said. “No, there’s a shortage of people that technology would not replace. ASV will better help you offload your team to do something else. Pentera helps you free up your time for things more strategic to your business.”
Building a Road Map to Facilitate Exposure Reduction
With IT infrastructure constantly evolving and cyber threats moving faster and becoming increasingly automated, companies today are finding themselves to be in a “technology arms race,” as Maor put it.
“Everybody says they need better prevention, taller walls, thicker walls. Prevention, detection and response, a recovery plan,” he said. “Across this stack, validating that our stack actually meets its objective for the purpose it was added, not just at the point in time it was added, but three months after, two years after. Because, right now, your IT’s changing. We have a customer that has about 50 IT infrastructure changes a week.”
As a company, Pentera prides itself in maintaining the highest standards of customer satisfaction and loyalty, with a continuous feedback cycle which keeps the company attuned to clients’ cybersecurity needs in an age of rapidly evolving technology.
“We keep improving with the products,” Maor said. “Taking in new vulnerabilities, new attack frameworks, new TTPs and adding it to the product. Right now, with increased cloud adoption, many of our customers are challenged. ‘I have my team move, they are already there, (but) I have no idea if the stack I built holds any water in this hybrid model.’ How can the adversary potentially move from beyond one stack to a cloud infra because they have one leg in network and one leg out open externally. It’s a risk. Our clients use Pentera to evaluate that same risk.”
Another looming cybersecurity risk that Pentera is tackling head on is the growing threat of ransomware.
“Ransomware is top of mind. Everyone understands the impact,” Maor said. “Pentera has just launched a new functionality to our platform that’s called Ransomware Ready. We want to tell you ahead of time what your level of readiness is, as well as to evaluate its potential impact against a ransomware attack.”
Maor says he’s seen the ransomware strains out there, and he told us they’re hitting every door. And that’s the main reason Pentera emulated and built a ransomware attack framework. With this solution, businesses can run the Pentera ransomware emulation framework on their own infrastructure and emulate an end-to-end scenario from infection, encryption, to exfiltration.
“The need to validate your security from the perspective of an attacker looking outside in, or of an assumed breach inside-out approach, is something that is top of mind for us, and we’re focusing head on right now for our customers’ needs.”
HostingAdvice.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation from many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across the site (including, for example, the order in which they appear). HostingAdvice.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.
Our site is committed to publishing independent, accurate content guided by strict editorial guidelines. Before articles and reviews are published on our site, they undergo a thorough review process performed by a team of independent editors and subject-matter experts to ensure the content’s accuracy, timeliness, and impartiality. Our editorial team is separate and independent of our site’s advertisers, and the opinions they express on our site are their own. To read more about our team members and their editorial backgrounds, please visit our site’s About page.

